Managing Packages, Repositories, and Subscriptions with Ansible
Using Modules to Manage Packages
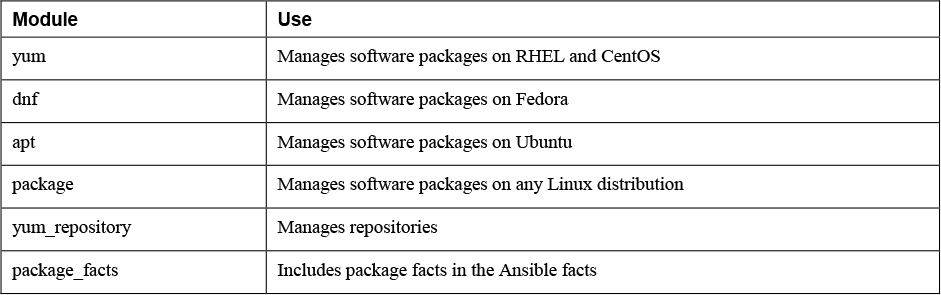
Modules used to manage packages:
Configuring Repository Access
The yum_repository module lets you work with yum repository files in the /etc/yum.repos.d/ directory.
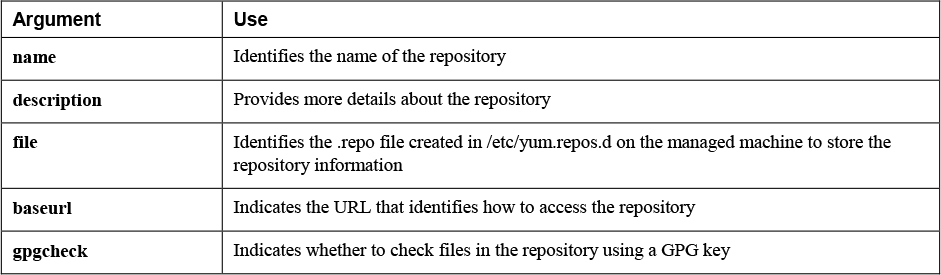
yum_repository Key Arguments
- gpgcheck argument is recommended but not mandatory.
- Most repositories are provided with a GPG key to verify that packages in the repository have not been tampered with.
- If no GPG key is set up for the repository, the gpgcheck parameter can be set to no to skip checking the GPG key.
Managing Software with yum
yum module
- Used to manage software packages.
- install, remove, or update packages.
- Individual packages, as well as package groups and modules.
Perform a System Update:
To prevent the wildcard from being interpreted by the shell, you must make sure it is placed between single quotes.
Use Yum package groups to install the Virtualization Host package group:
-
Name of the package group needs to start with an @ sign and the entire package group name needs to be put between single quotes.
-
state: latest insures they are installed if they have not been installed yet.
-
If they have already been installed, they are updated to the latest version.
-
Modules as listed by the Linux yum modules list command can be managed with the Ansible yum module also.
-
Working with yum modules is similar to working with yum package groups.
-
The main difference is that a version number and the installation profile are included in the module name.
Managing Package Facts
- When Ansible is gathering facts, package facts are not included.
- To include package facts as well, you need to run a separate task
package_facts module
- Facts that have been gathered about packages are stored to the ansible_facts.packages variable.
manager argument
- Specifies which package manager to communicate to.
- Default value of auto automatically detects the appropriate package manager and uses that.
- You can specify the package manager manually, using any package manager such as yum or dnf.
Install virt-manager and show the package facts:
Using Modules to Manage Repositories and Subscriptions
Setting Up Repositories
- A repository is a directory that contains RPM files, as well as the repository metadata, which is an index that allows the repository client to figure out which packages are available in the repository.
Ansible does not provide a specific module to set up a repository.
To set up an FTP-based repository on the Ansible control host, you need to accomplish the following tasks:
• Install the FTP package. • Start and enable the FTP server. • Open the firewall for FTP traffic. • Make sure the FTP shared repository directory is available. • Download packages to the repository directory. • Use the Linux createrepo command to generate the index that is required in each repository.
- yum module is used to download a single package.
download_only
-
Used to ensure that the package is not installed but downloaded to a directory.
-
Must specify where the package needs to be installed with download_dir argument. download_dir
-
Specify where to download to
-
Requires repository access. If repository access is not available, the fetch module can be used instead to download a file from a specific URL.
Managing GPG Keys
rpm_key module.
- to make sure the client knows where to fetch the repository key.
Doesn’t work because no GPG-protected repository is available:
Managing RHEL Subscriptions
redhat_subscription module
- enables you to perform subscription and registration in one task.
rhsm_repository module
- Enables you to add subscription manager repositories.
In Exercise 12-2 you are guided through the procedure of setting up your own repository and using it. This procedure consists of two distinct parts. In the first part you set up a repository server that is based on FTP. Because in Ansible you often need to configure topics that don’t have your primary attention, you set up the FTP server and also change its configuration. Next, you write a second playbook that configures the clients with appropriate repository access, and after doing so, install a package.
Setting Up a Repository
FTP Server
Client
Use the playbook to install redis:
ansible-playbook exercise122-client.yaml -e my_package=redis
Implementing a Playbook to Manage Software
https://github.com/sandervanvugt/rhce8-book/exercise123.yaml.
Add user and pass to vault:
To test:
ansible-playbook -C -k exercise123.yaml -e newhost=ansible5 -e newhostip=192.168.4.205
To run:
ansible-playbook -k --ask-vault-pass exercise123.yaml -e newhost=ansible5 -e newhostip=192.168.4.205 command. Everything
Lab 12-1
Configure the control.example.com host as a repository server, according to the following requirements:
• Create a directory with the name /repo, and in that directory copy all packages that have a name starting with nginx.
• Generate the metadata that makes this directory a repository.
• Configure the Apache web server to provide access to the repository server. You just have to make sure that the DocumentRoot in Apache is going to be set to the /repo directory.
Lab 12-2
Write a playbook to configure all managed servers according to the following requirements:
• All hosts can access the repository that was created in Lab 12-1.
• Have the same playbook install the nginx package.
• Do NOT start the service. Use the appropriate module to gather information about the installed nginx package, and let the playbook print a message stating the name of the nginx package as well as the version.
Practice exam task, edited.
This is a task from this practice exam. But edited for rhel9
https://repo.mysql.com/yum/mysql-8.4-community/el/9/x86_64/
Task 8: Software Repositories
Create a playbook /home/automation/plays/repository.yml that runs on servers in the database host group and does the following:
- A YUM repository file is created.
- The name of the repository is mysql84-community.
- The description of the repository is “MySQL 8.4 YUM Repo”.
- Repository baseurl is
https://repo.mysql.com/yum/mysql-8.4-community/el/9/x86_64/. - Repository GPG key is at
https://repo.mysql.com/RPM-GPG-KEY-mysql-2023. - Repository GPG check is enabled.
- Repository is enabled.